Build Security Into Your Organization, Not Just Your Tools
We assess your current posture, close the gaps, and train your people— creating lasting improvements, not one-time fixes.
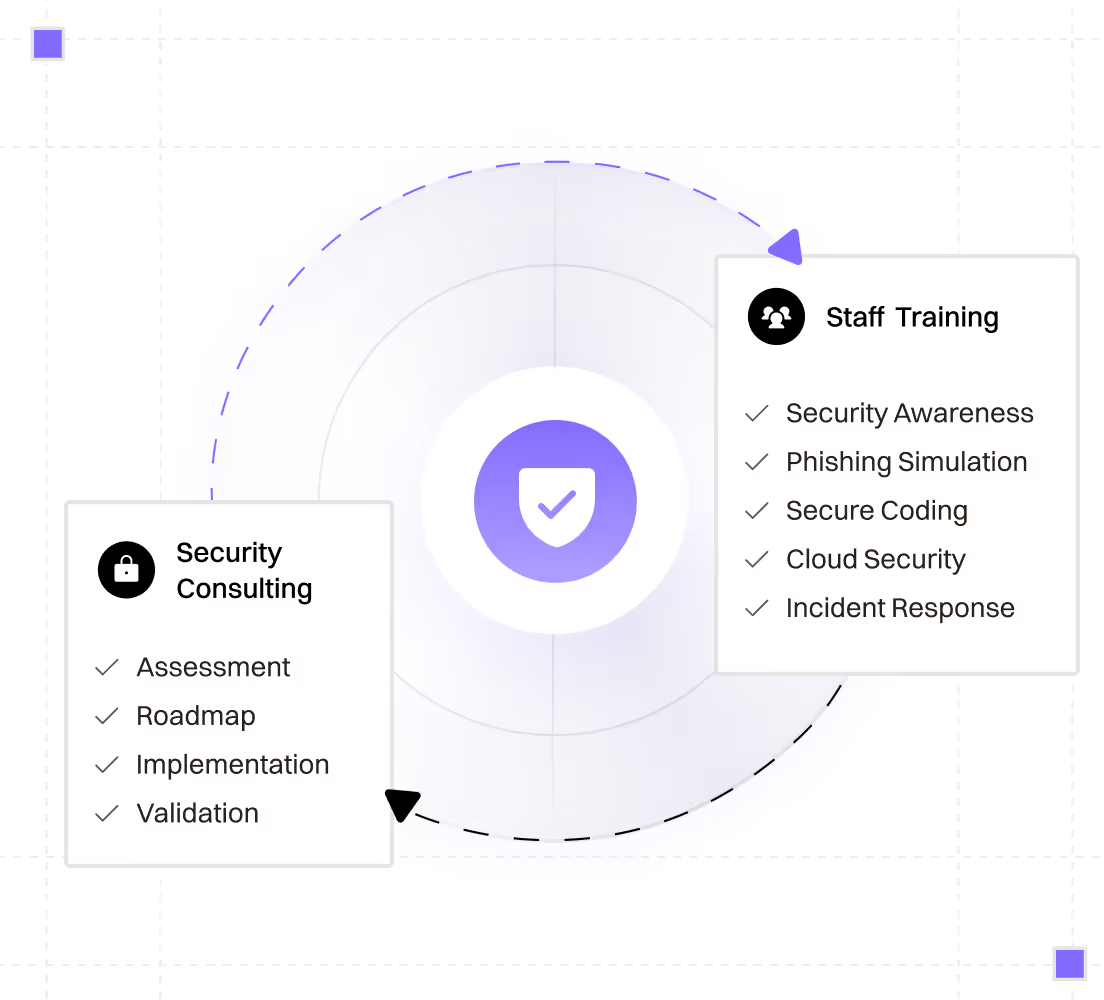

A structured engagement where we take ownership of improving your security posture. We identify what's missing, prioritize by risk, and drive implementation —not just recommendations in a PDF.
How it works
From first call to ongoing partnership in five simple steps.
Assessment
We review your infrastructure, workflows, and policies to understand your current state.
Roadmap
We deliver a prioritized plan based on risk and business impact.
Implementation
We work with your team (or independently) to close gaps.
Validation
We verify changes and document your improved posture.
Staff Training
Tools catch some threats. Trained people catch the rest. Most breaches still trace back to human decisions — clicking a link, misconfiguring a setting, or writing vulnerable code.
* All programs can be customized to your stack, industry, and compliance requirements.
Who This Is For
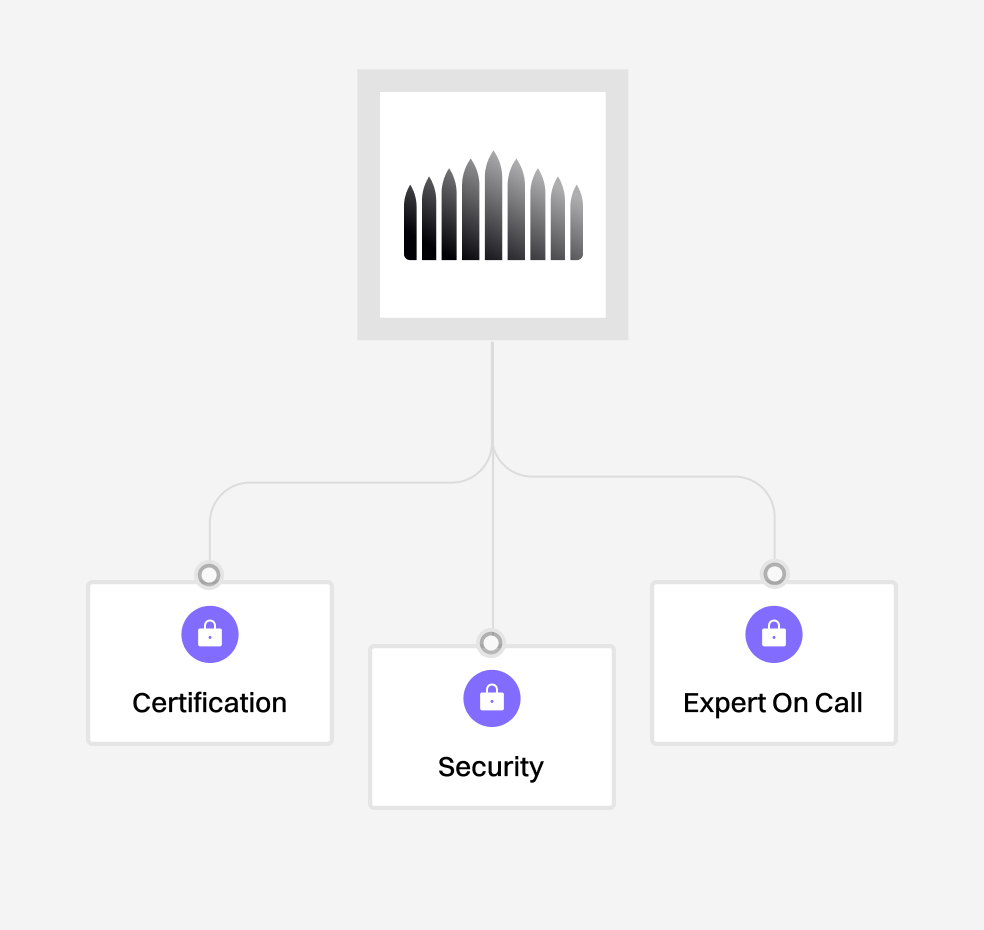
Preparing for certification
Organizations preparing for SOC 2, ISO 27001, or other certifications that need to close gaps before auditors arrive.
Growing fast, security lagging
Companies that have grown fast and know security hasn't kept pace — now it's time to catch up before problems arise.
Building proactive habits
Teams that want to reduce reliance on reactive fixes and build proactive security habits that stick.
Not sure where to start?
