Find Your Weaknesses Before Someone Else Does
Realistic, methodical testing across your applications, APIs, infrastructure, and AI systems - with clear findings you can act on.

We don't run a scanner and hand you a report. Our testers manually explore your systems the way real attackers would — combining automated tooling with hands-on techniques to find vulnerabilities that matter.
Every engagement gets a dedicated team matched to the scope and complexity of your environment. We pride ourselves on fast turnaround without compromising depth, and our pricing stays competitive — security testing shouldn't be a luxury reserved for enterprises with unlimited budgets.
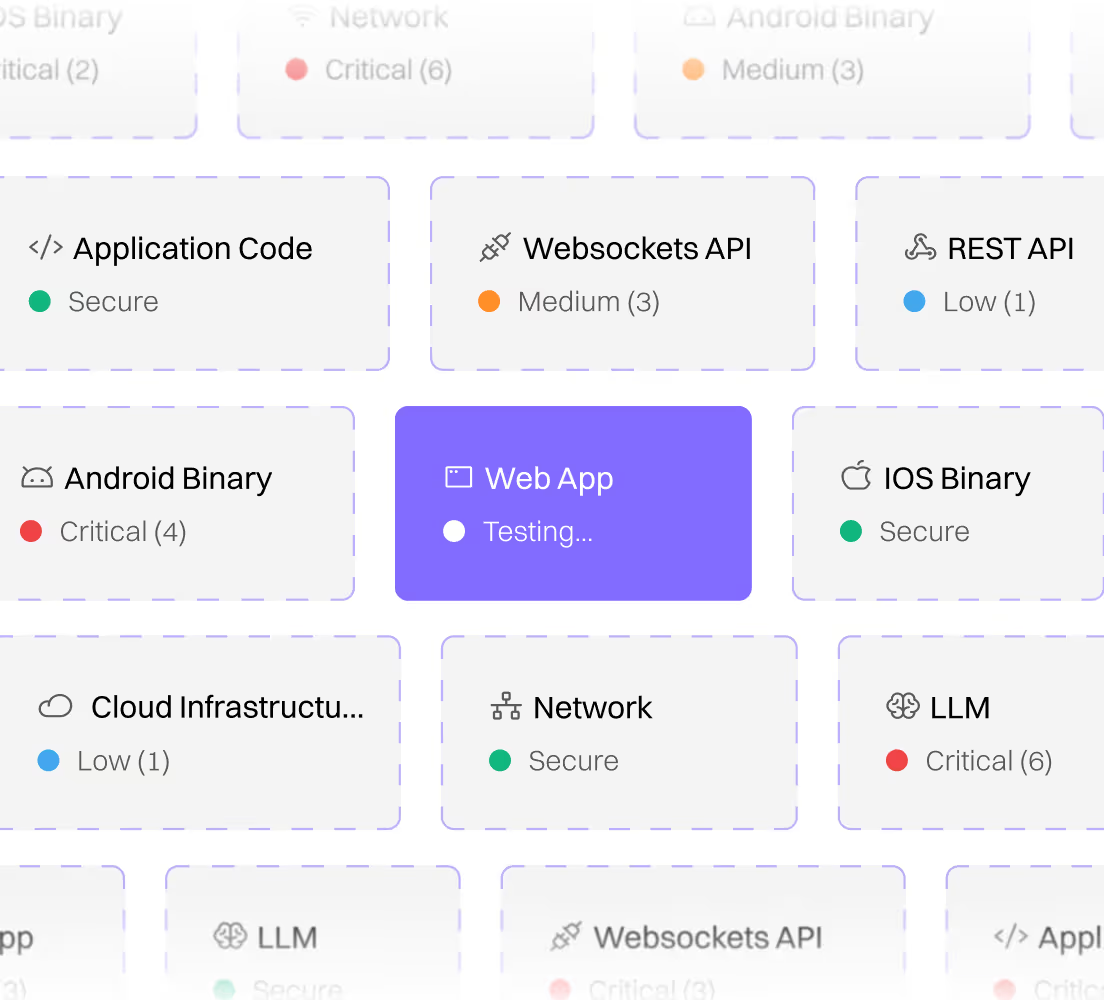
What We Test
Comprehensive coverage across your entire attack surface — from web applications to emerging AI systems.

Web Applications
Custom-built applications, CMS platforms, e-commerce sites, and SaaS products. We test for OWASP Top 10 issues and beyond—business logic flaws, authentication weaknesses, access control gaps, and more.

APIs
REST, gRPC, WebSockets, and GraphQL. We examine authentication, authorization, input validation, rate limiting, and data exposure risks.

Mobile Applications
Android and iOS. We review client-side security, local data storage, API communication, certificate handling, and reverse-engineering resilience.

Networks & Endpoints
Internal and external infrastructure assessments. We identify exposed services, misconfigurations, weak credentials, and lateral movement paths.
AI/LLM
A growing attack surface. We test for prompt injection, training data leakage, model manipulation, and insecure integrations with broader systems.
Deliverables
Clear, actionable outputs designed for both technical teams and executive stakeholders.
Executive Summary
High-level risk overview for leadership — key findings, overall security posture, and strategic recommendations.
Technical Report
Detailed findings with evidence, severity ratings, and step-by-step reproduction instructions for your engineering team.
Remediation Guidance
Practical recommendations prioritized by impact — so you know what to fix first and how to fix it effectively.
Retest
Validation that fixes were implemented correctly — confirming vulnerabilities are resolved before you move on.
Who This Is For
Launching new products
Companies launching new products or features that handle sensitive data and need confidence before going live.
Meeting compliance requirements
Organizations with compliance requirements mandating regular security testing — SOC 2, ISO 27001, PCI-DSS, and more.
Seeking external perspective
Teams that want an independent, external perspective on systems their internal team built — fresh eyes catch what familiarity misses.
Not sure where to start?
